MongoDB Atlas AWS IAM passwordless authentication example
MongoDB Atlas AWS IAM authentication mechanism allows users to use AWS IAM (Identity and Access Management) to establish a connection with MongoDB, which eliminates the need to manage and store passwords.
This mechanism generates a security token with a defined time-to-live, which ensures that access is limited and not taken advantage of for anything else. Additionally, the secret key is never directly passed to the MongoDB Atlas clusters and it’s never persisted by the Mongo driver, making it more secure.
In this article, we will walk through how to set up MongoDB Atlas AWS IAM passwordless authentication mechanism to connect to your MongoDB Atlas cluster using an EC2 instance.

Configure AWS environment
Let's get started by setting up the AWS environment.
Set up a VPC in AWS so that you can launch an instance in it.
Next, launch your instance and install MongoDB client in it. Follow the documentation here for installing MongoDB client.
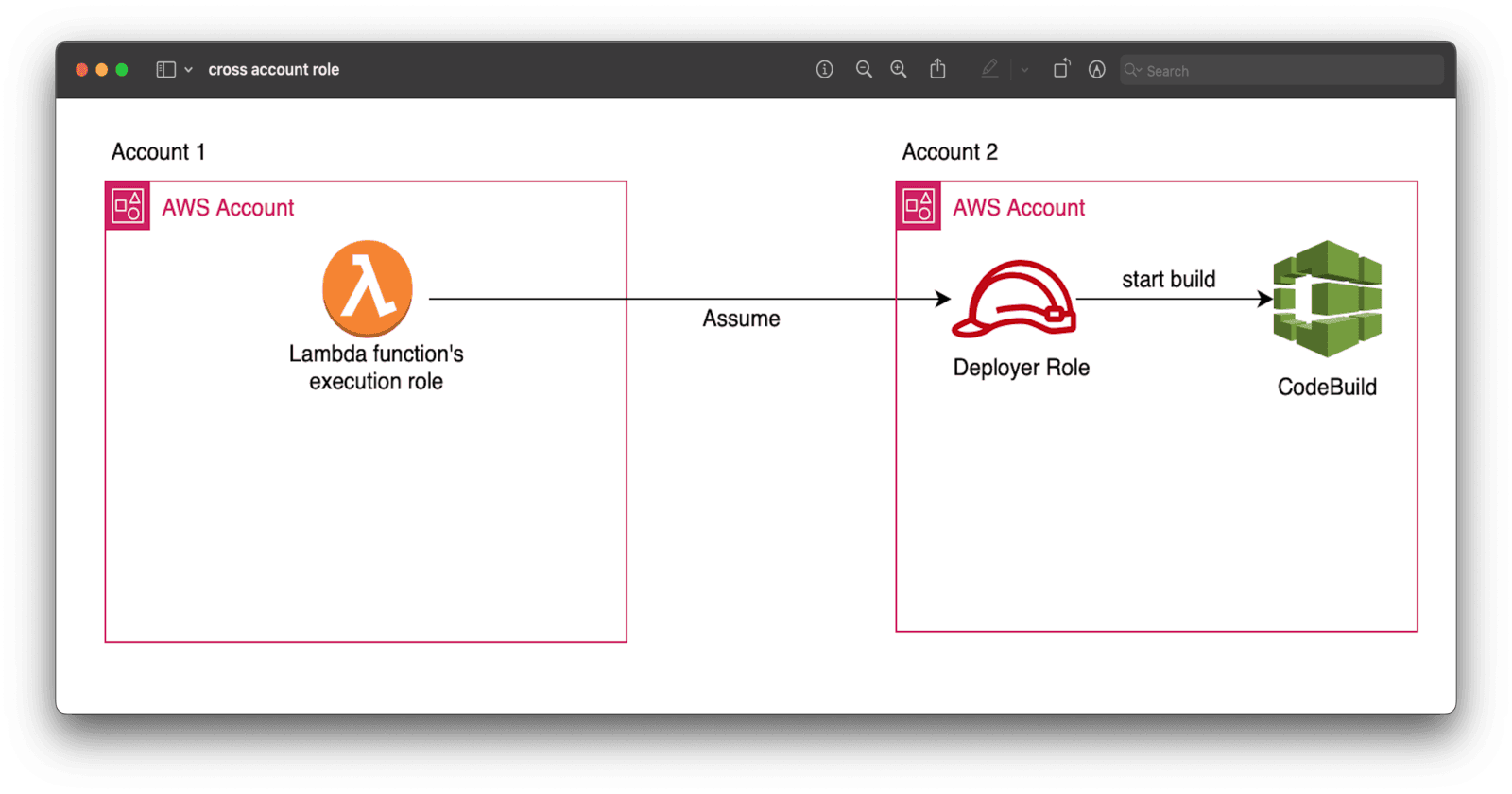
Create and attach an IAM role to this instance so that you can use the role to configure MongoDB-AWS IAM authentication and connect to the database from the instance.

Copy the ARN of the role you created so that we can start setting up MongoDB.
Great! You've set up your AWS environment. Let's now configure MongoDB Atlas to establish the connection.
Configure MongoDB Atlas
In the MongoDB Atlas dashboard, go to Database Access under Security and choose Add New Database User.

Next, Choose AWS IAM as your Authentication Method.
Select the IAM Role as AWS IAM type and paste the ARN you copied in Step 4 in the associated field. Then click Add user.

Testing the connection
Great. You've set up the connection. Now let's try connecting to our MongoDB and verify the connection works.
Go to the Database section in MongoDB console and click connect.

If you choose to connect your application to your cluster using MongoDB’s native drivers, you will be able to see a connection string format and notice that it has an AWS_SESSION_TOKEN in the end. This is a part of the temporary credentials that will be required when you try connecting to MongoDB.
Read the discussion here for more info.

As you already have an EC2 role assigned to the instance, you don't need to pass the temporary credentials. It'll be done automatically when you connect to the MongoDB cluster using the Mongo client.
SSH into your EC2 instance and run the command below after replacing db_url with appropriate value to connect to your Atlas cluster.
mongosh "mongodb+srv://<your_db_url>"
Voila! We can see that the connection is established.

MongoDB Atlas IAM connection using sts get-session-token
If you want to connect to your Atlas cluster from elsewhere, first make sure that you have the required permission to generate a session token and then run:
aws sts get-session-token --duration-seconds 900
This will generate temporary credentials which you can use for a fixed time (Here, 900 seconds) to connect to your cluster.
After you generate the credentials, replace <your_db_url>, <AWS access key>, <AWS secret key>, <session token (for AWS IAM Roles)> with the appropriate values and run the following command to establish the connection.
mongosh "mongodb+srv://<your_db_url>/?authSource=%24external&authMechanism=MONGODB-AWS" --apiVersion 1 --username <AWS access key> --password <AWS secret key> --awsIamSessionToken <session token (for AWS IAM Roles)>
Great job! Now you will be able to access your MongoDB Atlas cluster using AWS IAM passwordless mechanism.
Feel free to comment if you have any doubts in the article. Follow me for more cloud and DevOps content.
References:
MongoDB YouTube
Blog by Alfred J. Stanley.
MongoDB documentation
See you in cloud!
Vishnu S.